Don’t Fall For Firefox Banking Trojan Named “HoeflerText”
The malicious scam campaign, “The ‘HoeflerText’ font wasn’t found,” is back, which was previously targeting Google Chrome users to trick them into installing Spora ransomware on their computers.
This time the campaign has been re-designed to target Mozilla Firefox users with a banking trojan, called Zeus Panda, says Kafeine, a security researcher at Proofpoint.
Interestingly, the attackers behind this new campaign are so stupid that they forgot to change the name of the font, i.e. HoeflerText, due to which can be easily spotted.
As I previously warned — Next time when you accidentally land up on a suspicious website with jumbled content prompting to update the Firefox or Chrome font pack by downloading a missing text font to read the article… Just don’t download it. It’s obviously a trap.
Just like the previous one, the latest Firefox ‘HoeflerText font wasn’t found scam is also very convincing and easy to fall for.
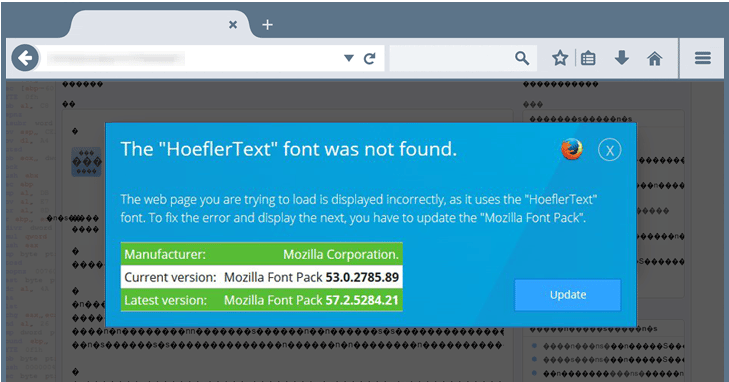
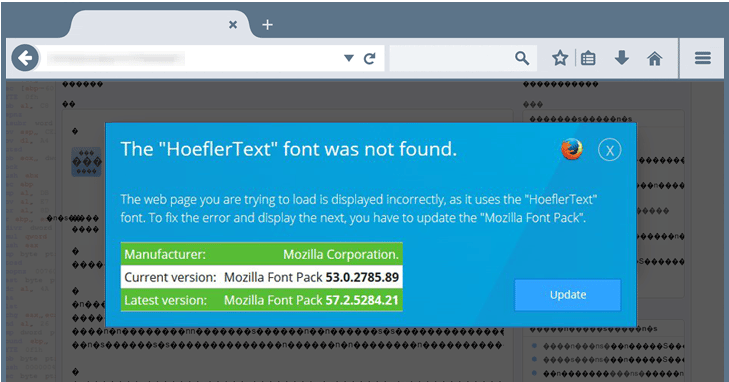
The attack initiates with an alert message, which states that “The ‘HoeflerText’ font was not found,” asking Firefox users to update their “Mozilla Font Pack.”
Once clicked, it downloads a ZIP file (Mozilla_Font_v7.87.zip) on the victim’s system, containing a JavaScript file. Meanwhile, the screen will display a set of instructions, asking victims to run the JS file in order to install the missing “Mozilla Font Pack.”
If the victims turned out to be so stupid that they run the JS file themselves, as instructed, the program will download the malware payload (.exe) from a remote server and then runs it automatically, injecting the Zeus Panda banking Trojan into the infected systems.
Panda is an online banking trojan that was initially found to be targeting banks in Europe and North America early last year and then started spreading itself to Brazil through at least three different exploit kits, including Angler, Nuclear, and Neutrino.
Once it infects a system, the Zeus Panda banking trojan contacts its command and control (C&C) server to send the infected device information, including a list of installed antivirus and firewall products.
Panda focuses on stealing banking credentials from users, as well as those of bitcoin exchanges, payment card services and online payments providers, prepaid cards, airline loyalty programs and online betting accounts, to name a few.
To protect yourself from such scams, always exercise caution when downloading anything from the Internet onto your computers. Moreover, keep your antivirus up-to-date and do not ever fall for scam asking you to update your Mozilla or Chrome font pack, as it already comes with everything you need.
Talk to us about better technology support for your business. We use a multitude of security layers to prevent issues like this from ruining your day or worse, your business. Contact us today.


